Listen to the large enterprise IT vendors for long enough, and you will hear that ‘best of breed’ solutions are a thing of the past. ‘The time when customers requiring a solution to a specific IT need should go out and seek the most capable tool and implement it in their environment has come and gone”, they say. These myopic and self-centered vendors will rail on and on about how; “yes there was a time when best of breed IT solutions were a great path forward, but that was before ‘we’ insert your favorite large monolithic software vendor here bought up all the best solutions and marketed them as a family of products already pre-integrated for our customers.” They will go on to say that “IT is so complicated and confusing that our customers should just buy all our products (and only our products) and all their problems will be solved!”
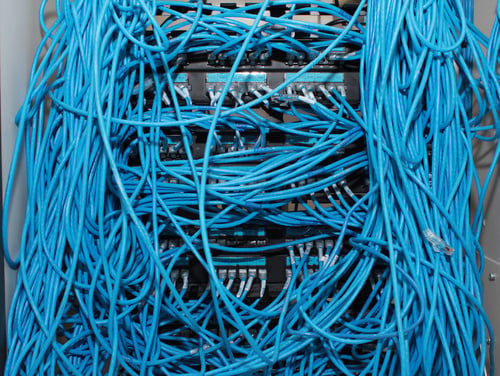
A solution suite has a lot of drag-along. It might seem simple, at first glance, but reality sets in quickly.
These same large vendors talk behind their customer’s backs about gaining a bigger share of the customer’s wallet—as if all of the more money they extract from their customers imparts more benefit the customer will accrue. (There is certainly benefit to the vendor when they have a stranglehold on the customer’s IT budget, but certainly much the opposite for the customer.) These vendors’ strategies are clearly to ignore the reality of the marketplace and where true innovation is happening, and to use any means necessary to convince customers that IT is easy if these customers “standardize” on their particular solution suite. “Don’t consider products from any other vendors (large or small)”, they will preach. “Your IT environment will only support your business needs by sending all of your IT budget my way and exclusively locking yourselves in to our products.”
The Reality Versus the Hot Air
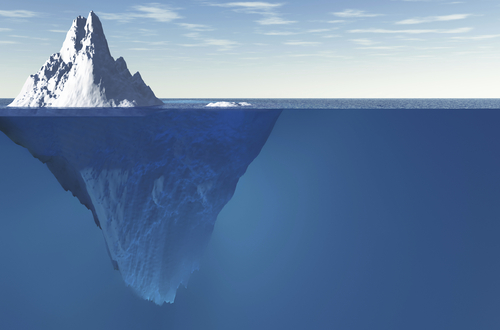
The reality of today’s dynamic markets is that standardization on a single vendor suite as being proposed by the large vendors is an impossibility for the modern enterprise.

Vendors are quick to tell you that unifying environments is as easy as selecting all of their tools. Tired of the hot air?
As companies merge and consolidate more rapidly, it is a certainty that the resulting entities will have a varied range of hardware and software solutions performing similar functions. Wholesale replacement of this technology to achieve homogeneity would be constant and costly while offering no real business benefit.
At the same time, the pace of technology change is rapid and uneven. An example is the recent innovation around network virtualization. The advent of network virtualization and Software Defined Networking (SDN) enables enterprises to examine how they might take advantage of this emerging technology to revolutionize data center architectures, not to mention ease the move to cloud-based technologies. Given that SDN technology is in its early stages, it is far from clear what implementation or vendor will emerge the leader in the space. Despite VMWare’s VMWorld 2013 announcement at about their NSX product (the bits that used to be Nicira), to date, nearly all of the larger vendors haven’t even developed a strategy much less a realistic product offering in this critical technical segment.
Independent Vendor Solutions and the Best of Breed Advantage
If standardization on a single vendor, and surrender of your IT budget is a non-starter, what does a successful approach look like, then?
The IT market today, perhaps more than ever before, presents a great range of best of breed technologies to select from. The fact is that most large vendors are working so hard to obscure this point. And they’re succeeding. The prospect of Cloud has the ability to give the choice and power back to the customer.
Cloud is much more than a way to provision and manage IT resources. The correct cloud manager enables enterprises to unify a heterogeneous environment (Hardware, Software private cloud and public cloud) to take advantage of best of breed solutions and increase the agility of the IT department to incorporate new and disruptive solutions. An independent cloud management tool can’t afford to be limited (or biased) in its support for internally deployed IT technologies (be they hardware or software) or in its support for various private or public cloud resources.
Why does vendor independence matter? Because an independent cloud platform is not beholden to making one IT technology or tool (or suite of tools) look or function better than any other. A truly independent and advanced cloud platform takes it cue from the market and supports those underlying tools and technologies demanded by the market and it’s customers.
In light of these requirements, examine the existing cloud management options, and you will find an independent vendor will provide significant advantage to your enterprise. Adoption of the proper independent solution makes best of breed technology easy to implement in your environment and provides a degree of agility and efficiency superior to standardizing on any single vendor.
Implement an independent cloud manager, and regain the power to chose the best of breed solution for each of your enterprise IT problems.
Want to learn more about what CloudBolt can do in your IT environment, regardless of your underlying technology choices or platform selection? We'd love to show you.